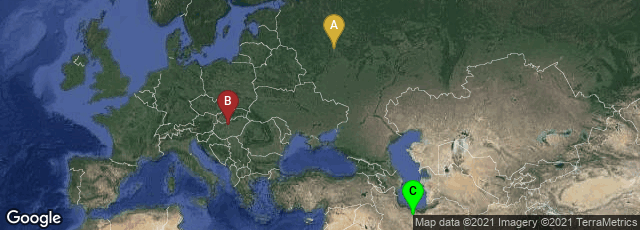
A: Tsentralnyy administrativnyy okrug, Moskva, Russia, B: XI. kerület, Budapest, Hungary, C: Iran, Tehran
On May 28, 2012 the MAHER Center of the Iranian National Computer Emergency Response Team (CERT), Kaspersky Lab headquartered in Moscow, and Cry SyS Lab (Laboratory of Cryptography and National Security) of the Budapest University of Technology and Economics announced the discovery of Flame malware that attacked computers running the Microsoft Windows operating system. A virus that collected information, it was arguably the most complex malware ever found.
"According to estimates by Kaspersky, Flame has infected approximately 1,000 machines, with victims including governmental organizations, educational institutions and private individuals. As of May 2012, the countries most affected are Iran, Israel, Sudan, Syria, Lebanon, Saudi Arabia, and Egypt. . . .
"According to Kaspersky, Flame has been operating in the wild since at least February 2010. CrySyS reports that the file name of the main component had been observed as early as December 2007. However, its creation date cannot be determined directly, as the creation dates for the malware's modules are falsely set to dates as early as 1994. Computer experts consider it the cause of an attack in April 2012 that caused Iranian officials to disconnect their oil terminals from the Internet. At the time the Iranian Students News Agency referred to the malware that caused the attack as "Wiper", a name given to it by the malware's creator. However, Kaspersky Lab believes that Flame may be 'a separate infection entirely' from the Wiper malware. Due to the size and complexity of the program—described as "twenty times" more complicated than Stuxnet—the Lab stated that a full analysis could require as long as ten years. On 28 May, Iran's CERT announced that it had developed a detection program and a removal tool for Flame, and had been distributing these to 'select organizations' for several weeks " (Wikipedia article on Flame (malware) accessed 05-30-2012).